DOI:
https://doi.org/10.64539/msts.v2i1.2026.462Keywords:
Federated Learning, Intrusion Detection System, Temporal Convolutional Network, Energy-Efficient Computing, Differential Privacy, IoT Security, Distributed Machine LearningAbstract
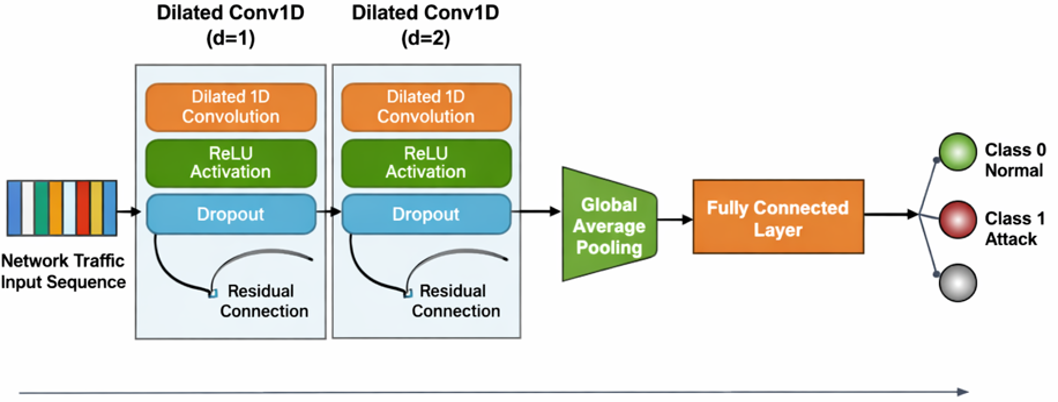
The rapid proliferation of Internet of Things (IoT) devices has significantly increased the attack surface of modern network infrastructures, necessitating intelligent and scalable intrusion detection systems. Federated Learning (FL) has emerged as a promising paradigm for distributed model training without centralized data sharing; however, challenges such as energy efficiency, data heterogeneity, and privacy preservation remain inadequately addressed. Existing studies often emphasize optimization objectives theoretically without validating them under realistic constraints. This paper proposes an energy-aware federated learning framework integrating Temporal Convolutional Networks (TCNs) for intrusion detection using distributed network traffic data. The framework incorporates differential privacy for secure model updates and a conceptual energy-aware client participation strategy. Experiments are conducted on the UNSW-NB15 dataset under a controlled setting with fixed client participation and communication parameters. The results demonstrate that the proposed model achieves improved classification accuracy and stable convergence behavior across communication rounds while operating under a fixed energy budget. However, energy consumption remains constant due to controlled experimental conditions, indicating that the study evaluates performance under energy constraints rather than dynamic energy optimization. The findings highlight the effectiveness of TCN-based federated models for intrusion detection in resource-constrained environments. Future work will focus on dynamic energy modeling, heterogeneous client environments, and comprehensive multi-objective evaluation.
References
[1] V. K. Pandey, D. Sahu, S. Prakash, R. S. Rathore, P. Dixit, and I. Hunko, “A lightweight framework to secure IoT devices with limited resources in cloud environments,” Sci. Rep., vol. 15, no. 1, Dec. 2025. https://doi.org/10.1038/S41598-025-09885-0.
[2] F. Cavallin and R. Mayer, “Anomaly Detection from Distributed Data Sources via Federated Learning,” Lecture Notes in Networks and Systems, vol. 450, pp. 317–328, 2022. https://doi.org/10.1007/978-3-030-99587-4_27.
[3] H. G. A. Umar et al., “Energy-efficient deep learning-based intrusion detection system for edge computing: a novel DNN-KDQ model,” Journal of Cloud Computing, vol. 14, no. 1, Dec. 2025. https://doi.org/10.1186/S13677-025-00762-9.
[4] G. Nassreddine, M. Nassereddine, and O. Al-Khatib, “Ensemble Learning for Network Intrusion Detection Based on Correlation and Embedded Feature Selection Techniques,” Computers, vol. 14, no. 3, Mar. 2025. https://doi.org/10.3390/COMPUTERS14030082.
[5] S. A. Oyedotun, G. P. Oise, and C. E. Ozobialu, “Towards Intelligent Cybersecurity in SCADA and DCS Environments: Anomaly Detection Using Multimodal Deep Learning and Explainable AI,” Journal of Science Research and Reviews, vol. 2, no. 3, pp. 20–31, Jul. 2025. https://doi.org/10.70882/josrar.2025.v2i3.76.
[6] M. Abd Elaziz, I. A. Fares, A. Dahou, and M. Shrahili, “Federated learning framework for IoT intrusion detection using tab transformer and nature-inspired hyperparameter optimization,” Front. Big Data, vol. 8, 2025. https://doi.org/10.3389/FDATA.2025.1526480.
[7] H. Alkahtani and T. H. H. Aldhyani, “Botnet Attack Detection by Using CNN-LSTM Model for Internet of Things Applications,” Security and Communication Networks, vol. 2021, 2021. https://doi.org/10.1155/2021/3806459.
[8] G. P. Oise, B. S. Olanrewaju, O. A. Orukpe, K. C. Pius, and A. O. Airhiavbere, “A Convolutional Neural Network Framework for Intelligent Intrusion Detection,” Scientific Journal of Computer Science, vol. 2, no. 1, pp. 50–59, Feb. 2026. https://doi.org/10.64539/sjcs.v2i1.2026.404.
[9] G. P. Oise et al., “Isolation Forest–Based Intrusion Detection for Cyber-Physical Systems,” Scientific Journal of Engineering Research, vol. 2, no. 2, pp. 222–233, Mar. 2026. https://doi.org/10.64539/sjer.v2i2.2026.434.
[10] J. Kim, M. Shim, S. Hong, Y. Shin, and E. Choi, “Intelligent detection of IoT botnets using machine learning and deep learning,” Applied Sciences (Switzerland), vol. 10, no. 19, pp. 1–22, Oct. 2020. https://doi.org/10.3390/app10197009.
[11] D. C. Attota, V. Mothukuri, R. M. Parizi, and S. Pouriyeh, “An Ensemble Multi-View Federated Learning Intrusion Detection for IoT,” IEEE Access, vol. 9, pp. 117734–117745, 2021. https://doi.org/10.1109/ACCESS.2021.3107337.
[12] G. P. Oise, O. C. Nwabuokei, O. J. Akpowehbve, B. A. Eyitemi, and N. B. Unuigbokhai, “Towards Smarter Cyber Defense: Leveraging Deep Learning for Threat Identification and Prevention,” FUDMA Journal of Sciences, vol. 9, no. 3, pp. 122–128, Mar. 2025. https://doi.org/10.33003/fjs-2025-0903-3264.
[13] M. M. Forootan, I. Larki, R. Zahedi, and A. Ahmadi, “Machine Learning and Deep Learning in Energy Systems: A Review,” Sustainability (Switzerland), vol. 14, no. 8, Apr. 2022. https://doi.org/10.3390/SU14084832.
[14] O. Shahid, V. Mothukuri, S. Pouriyeh, R. M. Parizi, and H. Shahriar, “Detecting Network Attacks using Federated Learning for IoT Devices,” Proceedings - International Conference on Network Protocols, ICNP, 2021. https://doi.org/10.1109/ICNP52444.2021.9651915.
[15] P. Madan, V. Singh, D. P. Singh, M. Diwakar, B. Pant, and A. Kishor, “A Hybrid Deep Learning Approach for ECG-Based Arrhythmia Classification,” Bioengineering, vol. 9, no. 4, Apr. 2022. https://doi.org/10.3390/bioengineering9040152.
[16] V. Rey, P. M. Sánchez Sánchez, A. Huertas Celdrán, and G. Bovet, “Federated learning for malware detection in IoT devices,” Computer Networks, vol. 204, no. 21, Feb. 2022. https://doi.org/10.1016/j.comnet.2021.108693.
[17] E. M. Campos et al., “Evaluating Federated Learning for intrusion detection in Internet of Things: Review and challenges,” Computer Networks, vol. 203, pp. 298–301, Feb. 2022. https://doi.org/10.1016/j.comnet.2021.108661.
[18] N. B. Unuigbokhai et al., “Advancements In Federated Learning for Secure Data Sharing in Financial Services,” FUDMA Journal of Sciences, vol. 9, no. 5, pp. 80–86, May 2025. https://doi.org/10.33003/fjs-2025-0905-3207.
[19] B. Olanrewaju-George and B. Pranggono, “Federated learning-based intrusion detection system for the internet of things using unsupervised and supervised deep learning models,” Cyber Security and Applications, vol. 3, p. 100068, Dec. 2025. https://doi.org/10.1016/J.CSA.2024.100068.
[20] B. Wu, “A Wavelet-Based Derivative-Aware Transformer for Network Intrusion Detection,” in 2025 22nd International Computer Conference on Wavelet Active Media Technology and Information Processing (ICCWAMTIP), IEEE, Dec. 2025. https://doi.org/10.1109/ICCWAMTIP68645.2025.11352641.
[21] G. P. Oise, “E-ViTNet: A lightweight vision transformer with oppositional cat swarm optimization for automated E-Waste sorting,” Next Research, vol. 6, p. 101373, Apr. 2026. https://doi.org/10.1016/j.nexres.2026.101373.
[22] G. Oise and S. Konyeha, “Environmental impacts in e-waste management using deep learning,” Discover Artificial Intelligence, vol. 5, no. 1, p. 210, Aug. 2025. https://doi.org/10.1007/s44163-025-00376-9.
[23] B. Wu, “A Wavelet-Based Derivative-Aware Transformer for Network Intrusion Detection,” in 2025 22nd International Computer Conference on Wavelet Active Media Technology and Information Processing (ICCWAMTIP), IEEE, Dec. 2025. https://doi.org/10.1109/ICCWAMTIP68645.2025.11352641.
[24] Y. Wang, “A Network Intrusion Detection Method Based on Parameter Optimization and Transformer,” in 2026 International Conference on Communication Networks and Machine Learning (CNML), IEEE, Jan. 2026, pp. 56–60. https://doi.org/10.1109/CNML68938.2026.11453115.
[25] G. P. Oise, T. Jessa, E. Mintah, F. O. Uloko, O. Sokoya, and O. Ukpebor, “A Hybrid Machine Learning–Optimization Framework for Energy Demand Forecasting and Decision Support in Smart Infrastructure,” Methods in Science and Technology Studies, vol. 2, no. 1, pp. 68–81, Apr. 2026. https://doi.org/10.64539/msts.v2i1.2026.440.
[26] E. N. Yolaçan and H. Çavşı Zaım, “Temporal Windowed and Internal Feature (TWIF) Transformer for Attack Detection in Robotics,” IEEE Access, vol. 14, pp. 42674–42690, 2026. https://doi.org/10.1109/ACCESS.2026.3674720.
[27] U. C. Akuthota and L. Bhargava, “Transformer-Based Intrusion Detection for IoT Networks,” IEEE Internet Things J., vol. 12, no. 5, pp. 6062–6067, Mar. 2025. https://doi.org/10.1109/JIOT.2025.3525494.
[28] M. Roopak, G. Y. Tian, and J. Chambers, “An Intrusion Detection System Against DDoS Attacks in IoT Networks,” 2020 10th Annual Computing and Communication Workshop and Conference, 2020. https://doi.org/10.1109/CCWC47524.2020.9031206.
[29] M. H. Kabir, M. S. Rajib, A. S. M. T. Rahman, Md. M. Rahman, and S. K. Dey, “Network Intrusion Detection Using UNSW-NB15 Dataset: Stacking Machine Learning Based Approach,” in 2022 International Conference on Advancement in Electrical and Electronic Engineering (ICAEEE), IEEE, Feb. 2022. https://doi.org/10.1109/ICAEEE54957.2022.9836404.
[30] A. Almomani et al., “Phishing Website Detection With Semantic Features Based on Machine Learning Classifiers: A Comparative Study,” Int. J. Semant. Web Inf. Syst., vol. 18, no. 1, Jan. 2022. https://doi.org/10.4018/ijswis.297032.
[31] R. Ma, Q. Wang, X. Bu, and X. Chen, “Real-Time Detection of DDoS Attacks Based on Random Forest in SDN,” Applied Sciences (Switzerland), vol. 13, no. 13, Jul. 2023. https://doi.org/10.3390/app13137872.
[32] W. David, “UNSW_NB15,” 2019, The IXIA PerfectStorm tool. Australian Centre for Cyber Security (ACCS). https://www.kaggle.com/datasets/mrwellsdavid/unsw-nb15.
[33] S. Ahmed et al., “Effective and Efficient DDoS Attack Detection Using Deep Learning Algorithm, Multi-Layer Perceptron,” Future Internet, vol. 15, no. 2, Feb. 2023. https://doi.org/10.3390/fi15020076.
[34] R. Latha and R. M. Bommi, “Hybrid CatBoost Regression model based Intrusion Detection System in IoT-Enabled Networks,” Proceedings of the 9th International Conference on Electrical Energy Systems, 2023. https://doi.org/10.1109/ICEES57979.2023.10110148.
[35] G. Guo, X. Pan, H. Liu, F. Li, L. Pei, and K. Hu, “An IoT Intrusion Detection System Based on TON IoT Network Dataset,” 2023 IEEE 13th Annual Computing and Communication Workshop and Conference, 2023. https://doi.org/10.1109/CCWC57344.2023.10099144.
[36] Z. Liu, N. Thapa, A. Shaver, K. Roy, X. Yuan, and S. Khorsandroo, “Anomaly detection on lot network intrusion using machine learning,” 2020 International Conference on Artificial Intelligence, Big Data, Computing and Data Communication Systems, icABCD 2020 - Proceedings, Aug. 2020. https://doi.org/10.1109/icABCD49160.2020.9183842.
[37] Z. H. Abdaljabar, O. N. Ucan, and K. M. Ali Alheeti, “An Intrusion Detection System for IoT Using KNN and Decision-Tree Based Classification,” International Conference of Modern Trends in ICT Industry: Towards the Excellence in the ICT Industries, MTICTI 2021, 2021. https://doi.org/10.1109/MTICTI53925.2021.9664772.
[38] S. K. Kodali and C. H. Muntean, “An Investigation into Deep Learning Based Network Intrusion Detection System for IoT Systems,” Proceedings of 2021 IEEE International Conference on Data Science and Computer Application, ICDSCA 2021, pp. 374–377, 2021. https://doi.org/10.1109/ICDSCA53499.2021.9650111.
[39] P. O. Adebayo, M. Jubrin Abdulahi, O. M. Lawrence, Y. A. Ibrahim, S. A. Faki, and B. A. Hassan, “An Artificial Intelligence-based Ensemble Technique for Intrusion Detection and Prevention in IoT Systems,” International Conference on Science, Engineering and Business for Driving Sustainable Development Goals, SEB4SDG 2024, 2024. https://doi.org/10.1109/SEB4SDG60871.2024.10629681.
[40] M. Ramaiah and M. Y. Rahamathulla, “Securing the Industrial IoT: A Novel Network Intrusion Detection Models,” 2024 3rd International Conference on Artificial Intelligence for Internet of Things, AIIoT 2024, 2024. https://doi.org/10.1109/AIIoT58432.2024.10574728.